SharePoint Framework is the new King of enterprise solutions. Since version 1.4.1, it allows you to easily connect to APIs secured with Azure Active Directory.
As a SharePoint developer, you will likely have to create Azure Web Apps or Functions to be consumed by your SharePoint Framework application. So why not use an ARM template for common scenarios?
The following ARM template will, hopefully, come in handy and save you some time.
UPDATE: unfortunately all images from this post were lost when I had to migrate the blog content. Hope things still make sense…
Despite the SharePoint mention, this template is completely generic and has no dependencies on SharePoint. You can use it for any work that uses a web application.
You can get the source code from my ARM Templates repository on GitHub
Resources
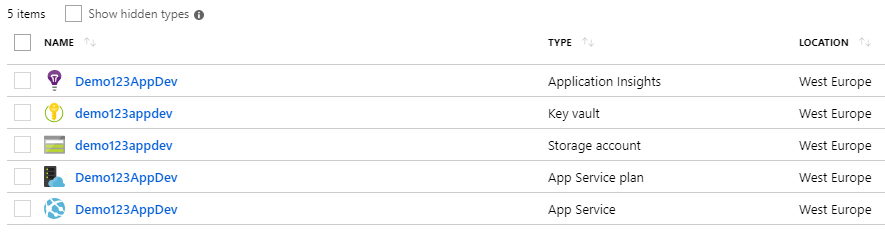
The following Azure resources are deployed:
- Application Insights
- Storage Account (and container)
- App Service
- Web Application
- Key Vault
Parameters
The following parameters can be configured for the template via the parameters.json file:
- userId – the Id of the admin user deploying the template
- components_Insights_name – the name of the Application Insights resource
- vaults_KeyVault_name – the name of the Key Vault resource
- storageAccounts_name – the name of the Storage Account resource
- storageAccounts_Container1_name – the name of the sample storage container
- serverfarms_AppService_name – the name of the App Service resource
- serverfarms_AppService_skuName – the SKU name to use for the App Service
- serverfarms_AppService_skuCapacity – the SKU capacity to use for the App Service
- sites_WebApp_name – the name of the Web Application resource
- sites_WebApp_kind – the kind of Web Application to create (app or API)
- sites_WebApp_clientId – the client Id of the Azure AD App Registration to use for authentication
- hostNameBindings_WebApp_name – the host bindings for the web application
- secrets_KeyVaultSecret1_name – the name of the sample secret to create on Key Vault
Configurations
The following configurations are included on the ARM template:
Location
All resources use the same location as the Resource Group. Ensure that all resource types are available in a given location before deploying.
Storage
The storage account is deployed with a sample “logs” container, in case you want to use it for logging.
Authentication
Azure Active Directory authentication is configured by default. This is done using the Client Id of an Azure AD App Registration that you provide as a parameter to the template.
Logging
Logging uses the file system as default and application logs are turned on. Please remember that logs are automatically turned off after 24 hours. There are retention policies for 90 days or 100 Mb.
Due to additional complexity around shared access signatures via ARM templates, I decided to use the file system as default for logging, but you can manually switch to use the logs container provided.
Key Vault
We do not add any sensitive information to the parameters file. We input a sample secret during deployment that is added as a Secret to the Key Vault.
Access policies are set so that the Web App is given Get permissions (using Managed Service Identity) to read Key Vault Secrets and the user running the script is given full access to the Key Vault.
Web App extensions
The Application Insights extension is added to the Web App. If you are deploying a .Net application, make sure you enable it.
Web App settings
The following settings are being set during deployment:
- APPINSIGHTS_INSTRUMENTATIONKEY – the instrumentation key required to connect Application Insights with the Web App
- StorageConnectionString – storage account connection string
- AzureWebJobsDashboard – storage account connection string
- AzureWebJobsStorage – storage account connection string
- keyVaultSecret1 – a sample entry containing the URL to the Key Vault secret created during deployment
Deployment
Before you deploy the script, ensure that you update the parameters.json file to your needs.
You can use the following PowerShell commands to retrieve the subscription Id and User Id required for the deployment:
- Connect-AzureRmAccount
- Get-AzureRmSubscription
- Get-AzureRmADUser -Mail ‘{AzureAdminEmailAddress}’
Additionally, an Azure Active Directory App Registration is required in order to configure Authentication. Please access the Azure Portal and create one. Copy the Client Id from the app registration to the parameters.json file. Alternatively, you can follow this blog post to create it using Azure CLI.
You can deploy the template using any of the deployment files provided for your platform of choice by passing the required parameters to it.
The following example demonstrates how to deploy using PowerShell:
.\deploy.ps1 -subscriptionId "XXXXXXXX-XXXX-XXXX-XXXX-XXXXXXXXXXXX" -resourceGroupName "Demo123AppDev" -resourceGroupLocation "West Europe" -deploymentName "Demo123AppDev" -templateFilePath "template.json" -parametersFilePath "parameters.json"After the deployment script runs, you need to access your Web App and enable Authentication/Authorization for Azure Active Directory as this is not part of the script (yet).
Feedback
Please submit feedback if you think something important is missing. This is a basic version intended to be a starting point to evolve over time based on feedback and client projects.
I hope you find the template easy to use and adapt to your needs. You can easily also replace the Web Application with a Function if that is what you need or simply add a database to it.
Great post! thanks for the info. It helped me a lot on finding out how to deploy azure functions app settings from the ARM template 🙂
Btw, take into account that if you are using the free or shared tier of a az server farm, the app services may complain of the “alwaysOn” setting 😉